Executive Introduction
The year data breach 2026 represents a decisive turning point for enterprise security, governance, and financial resilience.
What was once viewed as an IT problem has fully evolved into a board-level threat capable of erasing enterprise value overnight.
A decade ago, a security breach meant stolen credentials or a compromised server.
Today, the threat landscape reflects a global battlefield shaped by identity attacks, AI-powered intrusion, geopolitical escalation, misconfigured cloud environments, ransomware industrialization, and increasingly aggressive disclosure laws.
As organizations expand digital operations and embrace hybrid work, attackers are leveraging automation, deepfake social engineering, and adversarial AI to accelerate breach velocity and increase impact.
For CEOs, CFOs, CIOs, CTOs, and CISOs, the implications are profound: data breaches 2026 are no longer rare, unexpected events.
They are predictable outcomes of modern digital complexity.
Executives who align cybersecurity with financial stewardship, governance, and operational resilience will outperform competitors, reduce long-term expenditure, and earn stakeholder trust.
Those who treat security as an IT cost center will face escalating losses, regulatory penalties, and reputational damage that may be impossible to recover from.
The strategic question is no longer if an organization will face a security breach 2026, but how well it will prevent, detect, contain, and respond to it.
The Evolving Risk Landscape: From Data Leaks to Ransomware Attacks 2026
The modern threat landscape has shifted decisively away from perimeter-based intrusions toward identity-centric compromise, cloud breaches 2026, and supply chain infiltration.
Attackers have learned that breaching a network perimeter is no longer necessary when human behavior, cloud misconfigurations, or excessive permissions offer a more reliable entry point.
Identity has become the newest and most vulnerable perimeter—exploited through phishing, MFA fatigue, credential theft, OAuth app abuse, and unmanaged service accounts.
Data leaks 2026 increasingly originate from poorly governed SaaS environments, insufficient data classification, or misconfigured cloud storage systems.
These silent exposures often go undetected for months and trigger severe regulatory and reputational consequences.
Meanwhile, ransomware attacks 2026 have become more coordinated, automated, and financially devastating.
Adversaries now target backups, exfiltrate sensitive data before encryption, and launch double– or triple-extortion models that pressure organizations to pay multiple times.
Supply chain and third-party breaches remain among the fastest-growing vectors. Rather than targeting a fortified enterprise directly, attackers compromise smaller vendors, managed service providers, or cloud-based software platforms that serve many customers simultaneously.
These events can spread across multiple industries with unprecedented speed, reminiscent of SolarWinds, Log4j, and MOVEit—incidents that reshaped global security expectations.
Executives must understand that the landscape driving security breaches 2026 is not random. It is a predictable convergence of identity weakness, cloud complexity, and adversarial automation.
This requires a shift from reactive incident response to proactive resilience engineering across identity, data, cloud, and operational processes.
The Leading Causes of Data Breaches 2026
The root causes of data breach 2026 reflect systemic gaps in governance, architecture, and identity management rather than isolated technical failures. Executives must grasp these causes in business language to prioritize investments accurately.
One of the most significant drivers is web application vulnerabilities, especially in API-driven architectures. As organizations rapidly build digital services, security architecture often lags behind development velocity.
Unprotected APIs, unpatched components, and insufficient encryption expose sensitive systems to automated exploitation.
Misconfigured cloud environments remain the most common cause of large-scale cloud breaches 2026. Excessive permissions, unmanaged service principals, open storage containers, and incorrect network security groups collectively create an attack surface that adversaries scan continuously.
The scale and speed of cloud make misconfiguration inevitable without continuous governance and automated controls.
Weak identity governance remains the Achilles’ heel of the enterprise.
Compromised credentials, orphaned accounts, privilege creep, and failure to rotate keys or enforce conditional access policies are leading predictors of insider data breaches and external intrusions.
Identity governance failures also correlate directly with the cost of data breaches 2026, since attackers often leverage privileged access to accelerate data exfiltration.
Insider threats both malicious and unintentional have increased due to hybrid work, decentralized data access, and unsecured collaboration tools. Employees often move sensitive information into personal cloud storage, messaging apps, or unapproved SaaS platforms, inadvertently creating exposure pathways.
Finally, lack of Zero Trust adoption leaves organizations reliant on outdated perimeter-based controls. Zero Trust is not a technology but a governance and architecture philosophy that assumes compromise and enforces least privilege everywhere.
Enterprises slow to adopt it face exponentially higher breach impact and longer dwell times.
Executives who address these systemic issues holistically—not through fragmented tools but through identity, governance, automation, and cloud architecture—will significantly reduce risk.
The Cost of Data Breaches 2026: Financial, Operational, and Reputational Impact
For CFOs and board members, the most pressing question is no longer how breaches occur—but how much they cost and how preventable they are. The cost of data breaches 2026 continues to rise due to regulatory penalties, litigation, ransomware payments, operational downtime, and erosion of customer trust. Yet the most overlooked cost is the long-term operational and financial disruption that persists long after the incident.
Direct financial costs include breach investigation, forensics, containment, customer notifications, and system restoration. Regulatory penalties, especially under GDPR, HIPAA, and new state-level privacy laws, now escalate rapidly for delayed disclosure or insufficient safeguards.
In the United States, disclosure requirements for data breach 2026 will become even stricter, forcing executives to navigate legal exposure and public scrutiny simultaneously.
Operational costs include downtime of critical systems, loss of access to essential data, and interruption of customer services.
Productivity loss during a breach can cripple operations, especially when identity systems or cloud platforms are compromised. Supply chain disruptions are increasingly common as interconnected systems collapse under cascading failures.
Reputational damage may take years to recover and often leads to customer churn, contract renegotiations, or increased insurance premiums. Investors and partners increasingly weigh cybersecurity posture as part of corporate valuation.
Executives must recognize a pivotal reality: prevention offers a far higher ROI than remediation.
The average cost of data breach prevented by modern identity platform continues to demonstrate the financial advantage of strengthening identity governance, automating access control, and deploying adaptive authentication.
Why SMEs (500–5000 Employees) Are Now Prime Targets
US-based SMEs with 500–5000 employees sit at the intersection of attractive revenue, valuable data, and limited internal security resources. Attackers know that these organizations often rely on fragmented tools, understaffed IT teams, and incomplete cloud governance.
As SMEs accelerate digital operations, cloud sprawl expands rapidly: dozens of SaaS applications, multi-tenant collaboration platforms, remote workers with unmanaged devices, and decentralized identity systems.
Resource constraints limit the adoption of enterprise-grade security controls, especially in organizations with small IT teams or outsourced support. Hybrid work amplifies attack surfaces, while BYOD policies introduce unmanaged endpoints into the network.
Cloud misconfiguration and lack of identity governance create opportunities for attackers to move laterally without detection.
The misconception that SMEs are “too small to target” has evaporated. Breach patterns show that attackers often view SMEs as entry points into larger supply chains.
As a result, the financial, operational, and legal consequences of a breach disproportionately impact mid-market companies.
Enterprises in this segment must therefore adopt the mindset and discipline of larger organizations while using automation, identity platforms, and cloud governance to compensate for limited manpower.
Best Tools for Preventing Data Breaches 2026
Executives often ask: “What are the best tools to prevent data breaches 2026?” The answer lies not in selecting individual vendors but in deploying the right categories of solutions that map to identity, cloud, data, and operational resilience. The most effective breach prevention tools fall into the following strategic pillars.
Modern Identity Platforms (Entra ID, Okta, Ping) provide conditional access, adaptive authentication, centralized governance, automated role assignment, and risk-based access decisions. They significantly reduce credential-based attacks, which remain the leading cause of security breaches 2026.
Privileged Access Management (PAM) solutions enforce least privilege, isolate sensitive credentials, rotate secrets, and monitor privileged actions. PAM reduces lateral movement and limits the blast radius of compromised accounts.
Cloud Security Posture Management (CSPM) continuously scans cloud configurations, detects misconfigurations, enforces guardrails, and provides automated remediation. Given the prevalence of cloud misconfiguration breaches, CSPM is now essential for any cloud-dependent enterprise.
AI-driven threat detection and XDR platforms use machine learning to identify behavioral anomalies, credential misuse, insider threats, and early indicators of compromise. They reduce dwell time and accelerate response.
Insider risk analytics tools analyze behavioral patterns, data movement, and anomalous access to identify insider data breaches before they escalate.
Automated containment platforms orchestrate rapid response actions such as isolating endpoints, revoking access tokens, disabling compromised identities, or quarantining cloud resources.
Executives should not evaluate tools in isolation. Instead, the most effective breach prevention strategy blends identity, data security, cloud governance, and continuous monitoring into a unified security architecture.
Best Data Breach Response Services Companies: What Executives Should Expect in 2026
Search trends show growing interest in “best data breach response services companies”—a clear sign that executives increasingly view response as a specialized discipline requiring external expertise. As threats escalate, organizations need partners who can reduce dwell time, contain incidents quickly, and navigate regulatory disclosure requirements with precision.
The best response providers in 2026 offer:
- Highly trained incident responders with experience across ransomware, insider threats, cloud breaches, and identity compromise
- Rapid containment via identity lockdown, token revocation, endpoint isolation, and threat eradication
- Advanced forensics with ability to reconstruct attacker paths and identify root causes
- Legal and regulatory guidance for breach disclosure requirements 2026
- Support for breach communications, customer notifications, and board reporting
- Integration with Microsoft Defender, Sentinel, and Purview for accelerated investigation
Executives should expect response partners to operate with the urgency of a financial crisis team—because in 2026, a data breach is a financial crisis.
The best partners reduce the probability of regulatory penalties, restore operations faster, and limit long-term reputational damage.
Identity Platforms and Cost Reduction: Why Modern Identity Prevents Multi-Million Dollar Breaches
Identity is the cornerstone of enterprise risk reduction.
According to multiple studies, the average cost of data breach prevented by modern identity platform is substantial, especially when organizations replace legacy authentication with adaptive, cloud-based systems.
Identity breaches remain the most expensive and difficult to remediate due to lateral movement, privilege escalation, and data exfiltration.
Modern platforms, particularly Microsoft Entra ID, offer risk-based conditional access, governance workflows, entitlement management, and access reviews that systematically reduce attack surfaces.
When combined with MFA, passwordless authentication, and continuous access evaluation, identity platforms become the most financially impactful security investment for mid-market enterprises.
For CFOs, the business case is clear: identity modernization delivers quantifiable ROI by reducing breach likelihood, minimizing threat dwell time, and simplifying audit and compliance processes. Investments in identity are not purely technical—they are financial risk mitigation.
Microsoft Cybersecurity Breach Protection 2026: Identity, Threat Prevention, Data Protection, and Rapid Response
Microsoft’s integrated security ecosystem—Entra ID, Defender XDR, Purview, and Sentinel—offers comprehensive protection across identity, device, data, application, and cloud workloads.
As organizations expand hybrid environments and adopt multiple SaaS platforms, Microsoft’s unified approach becomes increasingly valuable.
Entra ID enforces adaptive access, identity governance, privileged identity management, and strong authentication. It eliminates many causes of identity compromise and insider data breaches.
Microsoft Defender XDR correlates alerts across endpoints, identities, email, SaaS, and cloud workloads, enabling rapid detection of breach patterns. Its automated response capabilities significantly reduce dwell time.
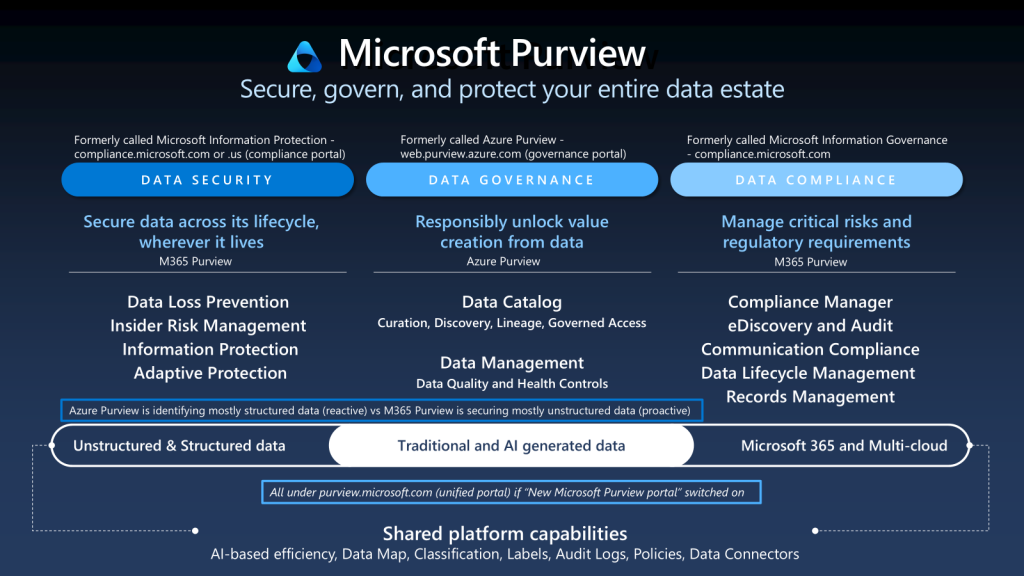
Microsoft Purview protects data across its entire lifecycle—classification, DLP, insider risk analytics, information protection, and auditing. Purview addresses both prevention and compliance obligations associated with breach disclosure requirements 2026.
Microsoft Sentinel delivers cloud-native SIEM and SOAR, accelerating investigation and providing deep visibility into cross-platform threats. Its ability to automate response workflows reduces operational burden on understaffed security teams.
Executives must understand that the strength of Microsoft cybersecurity breach protection lies not in individual tools but in the synergy of an integrated platform that centralizes identity, threat detection, governance, and response.
AI-Powered Prevention and Detection
AI will define the security landscape for data breach 2026. Adversaries already use generative AI to automate phishing, craft convincing lures, bypass MFA, and discover misconfigurations at scale. Enterprises must counter this with AI-driven defense.
AI-powered anomaly detection identifies deviations in user behavior, access patterns, or data movement long before a human analyst could detect them. Behavioral analytics reduce false positives and guide security teams toward high-risk anomalies.
Insider risk modeling uses machine learning to analyze sensitive data access, anomalous downloads, privilege escalation attempts, and off-hours activity. These models distinguish between normal work behavior and harmful intent.
Early warning systems correlate identity signals, device posture, cloud activity, and threat intelligence to detect breaches at their earliest stages.
When combined with automated containment, AI becomes a strategic advantage that reduces breach severity, cost, and dwell time.
Pre-Breach and Post-Breach Playbook for Executive Leaders
Executives require a structured approach that balances prevention, monitoring, response, and communication.
A strong pre-breach strategy includes identity modernization, cloud governance, data protection, and continuous monitoring.
Executives must set expectations for rapid escalation paths, cross-functional communication, and adherence to disclosure requirements.
Post-breach execution depends on incident containment, forensic investigation, and transparent communication with regulators, customers, and stakeholders.
Enterprises that respond effectively protect valuation, maintain trust, and reduce the likelihood of long-term consequences.
Leadership must treat cybersecurity as a component of operational continuity, financial stewardship, and brand reputation—not merely as technology oversight.
2026 Readiness Checklist for C-Level Leaders
Executives preparing for data breach 2026 must evaluate whether their organizations possess:
- A modern identity platform with adaptive access and governance
- Continuous cloud posture monitoring and automated remediation
- Full lifecycle data protection and insider risk analytics
- A hardened backup and recovery strategy resistant to ransomware
- AI-driven detection, response, and anomaly analysis
- Well-defined incident response plans with tested playbooks
- Assigned breach disclosure responsibilities and communication protocols
- A specialized breach response partner to reduce dwell time
- Visibility across identity, data, endpoint, SaaS, and cloud workloads
Organizations that operationalize these capabilities will outperform competitors, minimize risk, and enhance long-term financial resilience.
Conclusion
The realities of data breach 2026 demand a new form of executive leadership—one that blends financial discipline, technology insight, operational resilience, and strategic foresight.
Threat actors are faster, more automated, and more sophisticated than ever, exploiting identity weaknesses, cloud misconfigurations, data exposure, and supply chain vulnerabilities at unprecedented scale.
Organizations that remain reactive will face escalating financial, operational, and reputational damage.
Those who embrace proactive security—modern identity, integrated Microsoft protection, AI-driven detection, and continuous governance—will thrive in an increasingly hostile digital environment.
Enterprises that prepare now will enter 2026 with confidence, clarity, and competitive strength. In a world where breaches are inevitable but catastrophic failure is not, organizations with a strong security posture will outperform their peers, protect stakeholder value, and lead their industries into the next decade.


