From Wall Street to Main Street, we’ve created proprietary tools and products to ensure organizations are safe from cyber threats and compliant with all industry regulations and best practices.
HEALTHCARE COMPLIANCE AUDIT
The Office for Civil Rights (OCR) periodically performs audits on hospitals and medical practices to ensure the entities are compliant with all HIPAA standards. If any entity is found in violation of any of these standards, consequences may range from fines (ranging from $100 to $50,000 per offense) to litigation.
Exelegent performs a compliance audit and helps to create the foundation for an ongoing compliance program that thoroughly and completely reviews an entity’s compliance with all HIPAA standards (including the HITECH Act and Omnibus Rule revisions).
Our team of HIPAA compliance and network security experts have extensive experience in helping healthcare organizations implement and maintain simple, successful, and scalable information security and privacy programs, while helping to assess, achieve and maintain compliance with HIPAA, HITECH, and other states, federal, and international data safety regulations.
We use standards and frameworks previously developed and endorsed by various federal and international compliance and security organizations, including SANS, HITRUST, NIST, OCR, and The Department of HHS.
So, why perform Exelegent’s Healthcare Compliance Audit?
- Full audits reveal serious weaknesses and risks.
- Increasing number of settlements for privacy and security issues; expected increase in number of criminal cases
- Major HIPAA breaches have reached 1,000 milestones, with 1 in every 10 people in the US impacted.
- Cost of a breach is estimated at $188 per record. Average # of records per breach: 23,647 or $4.4M breach.
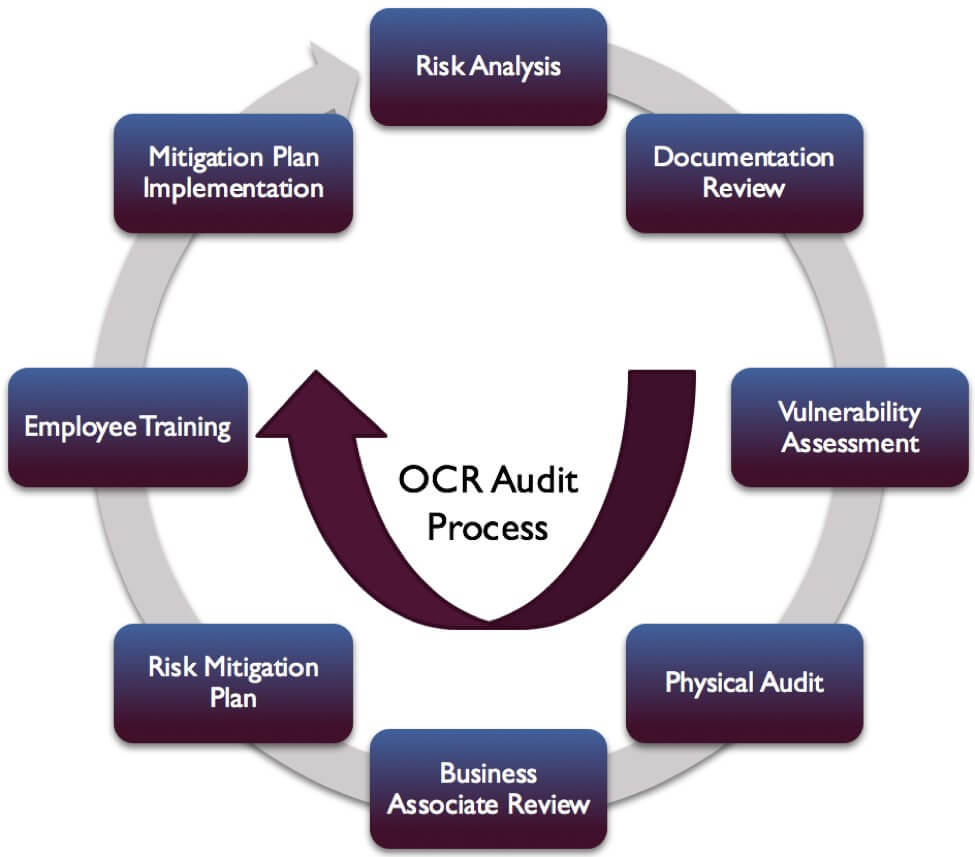
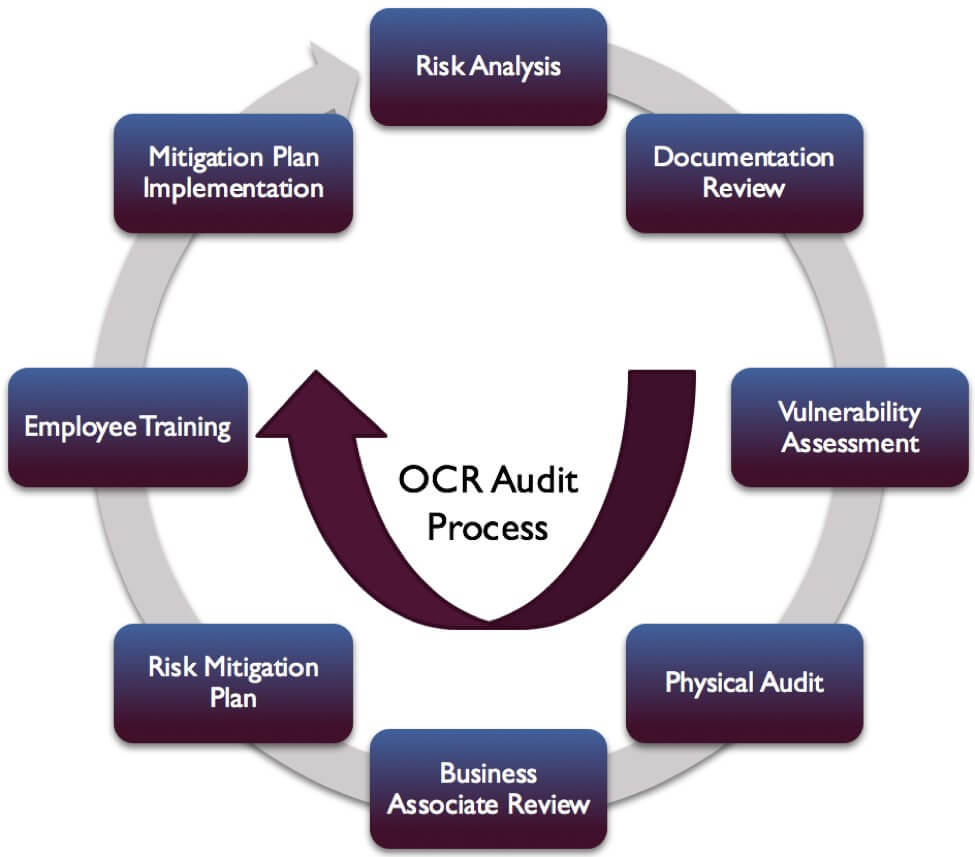
WHAT DOES IT LOOK LIKE?
A sample program
WHAT’S INCLUDED
- Mock OCR Audit
We proudly use the OCR phase II audit protocol to guide our healthcare compliance audits. This means that once complete, our audit will also serve as a mock OCR audit.
- Risk Analysis
A NIST-Based Risk Analysis is used to get a baseline. It is an exhaustive questionnaire of HIPAA rules and regulations that is an industry standard for enterprise healthcare organizations.
- Documentation Review and Update
With the help of our legal partners, we provide a comprehensive review of all HIPAA-related documentation. If necessary, documentation templates are also provided.
- Vulnerability Assessment and Penetration Testing
Using two industry-standard scanners, we test for any vulnerabilities in the organization’s network. Penetration testing is done separately at the customer’s request.
- Physical Audit
To test physical location security and employee awareness, Exelegent project managers anonymously visit client locations and look for ways to access protected health information.
- Business Associate Review
We do a basic review of the organization’s business associates who access, maintain, or modify PHI to ensure they are fully compliant with HIPAA.
- Risk Mitigation
The HIPAA Compliance process is nothing without mitigating all discovered risks. Our team helps to create an ongoing program with a risk mitigation plan including due dates, deliverables, and people or departments responsible.
- Employee Training
Exelegent uses its proprietary compliance training and testing platform, CertifyHIPAA.com, for employees to understand HIPAA in an easy-to-use way.
- Final Results and Findings
To summarize our audit and detail actionable next steps, we create a high-level final document that can be distributed to managers and stakeholders.
Our support doesn’t end when the audit ends
Exelegent’s HIPAA program is meant to be run so that organizations can continue maintaining compliance. Due to our automated processes, we’re able to help organizations with HIPAA compliance items that require periodic updates – like employee training, or risk analysis updates.
Exelegent prides itself on being able to keep your organization on top of its compliance, even when we’ve submitted our final reports. This way, we’re able to maintain an ongoing relationship with our customers and know how to best support them in the unfortunate and unlikely event of a breach.